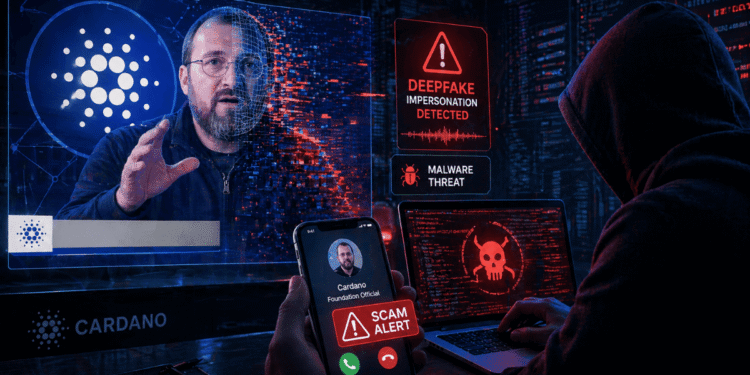
A crypto founder narrowly avoided a malware attack after joining a Microsoft Teams call with someone impersonating Cardano Foundation executive Pierre Kaklamanos, in what appears to be one of the latest examples of AI-powered social engineering targeting the crypto industry.
The attackers reportedly used convincing video and audio to make the meeting look legitimate. Two other supposed foundation staff members also appeared on the call, adding another layer of credibility. During the meeting, the victim was told to run a terminal command for a fake Microsoft Teams update, a common tactic used to install malware under the cover of a routine software fix.
The attack failed only because the victim’s laptop battery died before the process could be completed. That lucky interruption may have prevented a full device compromise.
How the Scam Worked
A Trusted Identity Became the Entry Point
The attack appears to have started through a communication channel that looked familiar to the victim. That detail matters because many crypto scams no longer begin with obvious spam links or poorly written messages.
Instead, attackers are increasingly using compromised accounts, revived old conversations, fake Calendly invites and impersonated executives to create trust before delivering the payload. In this case, the meeting appeared to involve a real Cardano Foundation figure, making the request feel more plausible.
The use of AI-generated video and audio made the deception much harder to spot. If a victim sees a familiar face, hears a familiar voice and believes they are in a normal business call, they may lower their guard at the exact moment they should be most careful.
The Fake Update Was the Malware Trigger
The key red flag was the terminal command. The attackers reportedly instructed the victim to run a command as part of a bogus Teams update.
That technique is dangerous because it bypasses the usual suspicion around downloaded files. Instead of sending an obvious attachment, attackers convince the target to copy and paste a command directly into their machine. Once executed, that command can download malware, open remote access, steal credentials, search for wallet files or compromise browser sessions.
For crypto founders, developers and treasury operators, that can be catastrophic. A compromised laptop may expose seed phrases, password managers, exchange sessions, multisig tools, API keys, developer credentials or internal project systems.
Cardano Ecosystem Figures Are Being Targeted
CryptoBriefing and other outlets have reported similar deepfake meeting attempts aimed at Cardano ecosystem participants. Minswap builders also warned about a pattern involving resurrected direct messages, AI-generated impersonation and urgent software-update prompts.
That suggests this was not a random one-off scam. It looks more like a targeted campaign against high-value crypto users, especially people with access to wallets, codebases, treasury systems or community influence.
Cardano may be the visible example here, but the threat is much broader. Any crypto team that relies on remote calls, Telegram coordination and fast-moving partnership discussions could be vulnerable.
Why Deepfakes Make Crypto Security Harder
Seeing Is No Longer Verifying
Crypto users are already trained to avoid suspicious links and fake airdrops. Deepfake calls create a harder problem because they attack human trust directly.
A video call used to be a strong verification step. If someone looked and sounded like the person you expected, that was usually enough. AI now weakens that assumption.
That does not mean every remote meeting is unsafe. It means crypto teams need stronger verification habits. A face on a screen should not be enough to approve software installs, wallet actions, transaction signing or terminal commands.
The Tactic Fits Broader DPRK-Linked Patterns
Security researchers have previously linked similar fake meeting and fake update attacks to North Korea-aligned campaigns targeting crypto firms. These operations often use Zoom or Teams-style calls, fake technical problems and software update prompts to push malware onto victims’ devices.
The goal is usually financial. Crypto companies and founders are attractive targets because one successful compromise can lead to stolen tokens, drained wallets or access to internal systems that support larger attacks.
Even if this specific incident has not been formally attributed, the tradecraft looks familiar: social engineering, impersonation, fake collaboration and malware delivery through a trusted business workflow.
What Crypto Teams Should Do Now
The main lesson is simple: no one should run terminal commands during a video call unless the request has been independently verified through a separate trusted channel.
Crypto teams should also use pre-agreed verification phrases for sensitive meetings, confirm unusual requests through a known phone number or secure internal channel and require a second person to approve any software installation during business calls.
Founders and developers should be especially careful with devices that touch wallets, multisig dashboards, exchange accounts or production infrastructure. Ideally, treasury activity should happen on hardened devices that are not used for casual meetings, Telegram chats or browsing.
Projects should also create internal rules for video-call identity checks. If a meeting involves a new partnership, grant discussion, foundation representative or investor, teams should verify the invite through official domains, known contacts and public channels before joining.
What Comes Next
The next thing to watch is whether the Cardano Foundation issues formal security guidance for ecosystem participants. Clear verification steps would help reduce confusion and make it harder for attackers to exploit the Foundation’s name.
Other major crypto projects should do the same. Deepfake scams are becoming good enough that informal trust is no longer sufficient, especially in an industry where one compromised device can lead to millions of dollars in losses.
The Cardano incident is a warning for the wider crypto market. AI has made impersonation cheaper, faster and more convincing. The defense is not panic. It is stricter verification, better device hygiene and a firm rule that no legitimate partner should ever pressure someone to run a terminal command during a meeting.
Disclaimer: This article is for informational purposes only and does not constitute financial, investment, or legal advice. Always conduct your own research before making any investment decisions.