That’s not meant to scare you. It’s just the reality of holding digital assets in 2026. Over $1.2 billion was stolen from crypto users and platforms in the first four months of this year alone. The Drift Protocol hack drained $295 million. The Kelp DAO exploit took $292 million. And just this week, Tether froze $515 million in stolen USDT across 371 wallets.
The threats are real, they’re growing, and they’re getting more sophisticated. But here’s the good news: the vast majority of crypto theft is preventable. The people who lose their funds almost always made one of a handful of avoidable mistakes.
This guide covers everything you need to know about keeping your crypto safe, whether you hold $500 or $500,000. No technical jargon. No unnecessary complexity. Just the practical steps that actually protect your money.
Step 1: Understand the Biggest Risks
Before you can protect yourself, you need to know what you’re protecting against. Crypto theft falls into a few main categories.
Exchange hacks. When a centralised exchange gets compromised, everyone with funds on that platform can lose money. This week’s Coinbase outage (caused by an AWS data centre overheating) is a reminder that exchanges are single points of failure. In the past, exchanges like FTX, Mt. Gox, and BitForex have collapsed entirely, taking billions in customer funds with them.
Smart contract exploits. When you use DeFi platforms, your funds interact with smart contracts, pieces of code that execute automatically on the blockchain. If that code has a vulnerability, hackers can drain it. The Drift and Kelp hacks both exploited weaknesses in bridge infrastructure, not user wallets.
Phishing and social engineering. This is the most common way individual users lose funds. A fake website, a fraudulent email, a scam message on Discord or Telegram pretending to be from customer support. You click a link, connect your wallet, approve a malicious transaction, and your funds are gone.
Seed phrase theft. Your seed phrase (the 12 or 24 words you received when you created your wallet) is the master key to everything. Anyone who has it controls your funds. No exceptions.
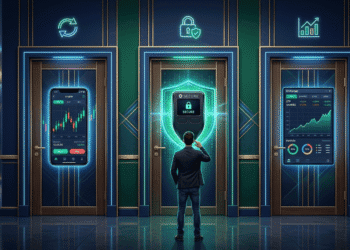
Step 2: Choose the Right Wallet
Your wallet is your first and most important line of defence. Choosing the right one depends on how much crypto you hold and how actively you trade.
For everyday use: A software wallet like Phantom, Solflare, or MetaMask is fine for day-to-day transactions and smaller amounts. These wallets run as browser extensions or mobile apps and connect easily to exchanges and DeFi platforms.
For long-term holdings: A hardware wallet like Ledger or Trezor stores your private keys on a physical device that never connects to the internet. This makes it nearly impossible for hackers to access your funds remotely. If you hold more than a few thousand dollars in crypto, a hardware wallet is strongly recommended.
The smart approach: Many experienced users run both. A software wallet for daily activity with smaller amounts, and a hardware wallet for long-term storage with the bulk of their holdings. That way, even if your software wallet is compromised, your main stack stays safe.
Step 3: Protect Your Seed Phrase Like Your Life Depends on It
This is the single most important rule in crypto security, and it’s the one people break most often.
Your seed phrase is the only way to recover your wallet if your device is lost, stolen, or destroyed. It’s also the only thing a thief needs to steal everything you own. There is no password reset. There is no customer support hotline. If someone else gets your seed phrase, your funds are gone permanently.
Write it down on paper. Not on your phone. Not in a screenshot. Not in your email drafts. Not in a cloud document. Paper. Physical, offline, unhackable paper.
Store it in a secure location. A fireproof safe, a safety deposit box, or split across two secure locations. Some people use metal seed phrase backup plates that survive fire and water damage.
Never share it with anyone. No legitimate company, exchange, wallet provider, or support team will ever ask for your seed phrase. If someone asks for it, they are trying to rob you. Full stop. No exceptions.
Never type it into a website. Phishing sites are designed to look exactly like real wallet interfaces. They ask you to “verify” or “restore” your wallet by entering your seed phrase. The moment you do, your funds are stolen automatically.
Step 4: Lock Down Your Accounts
Beyond your wallet, every account connected to your crypto activity needs to be secured properly.
Enable two-factor authentication (2FA) on everything. Every exchange account, every email address connected to crypto, every wallet that supports it. Use an authenticator app like Google Authenticator or Authy, not SMS-based 2FA. SIM swap attacks, where a hacker convinces your phone carrier to transfer your number to their device, can bypass SMS verification entirely.
Use unique passwords. A password manager like 1Password or Bitwarden generates and stores strong, unique passwords for every account. If you reuse passwords across sites and one of them gets breached, every account sharing that password is compromised.
Secure your email. Your email is the recovery mechanism for most of your accounts. If a hacker gains access to your email, they can reset passwords on exchanges and other platforms. Use a strong password, enable 2FA, and consider using a dedicated email address exclusively for crypto accounts.
Step 5: Be Smart About Exchanges
Exchanges are convenient but they come with risks. When your crypto sits on an exchange, you don’t actually control it. The exchange does. If the exchange gets hacked, goes bankrupt, or simply freezes withdrawals, your funds could be locked or lost.
Don’t store more than you need on exchanges. Keep only what you’re actively trading on the platform. Move the rest to a personal wallet where you control the keys.
Choose regulated exchanges. Platforms like Kraken (which just applied for a federal bank charter), Coinbase, and Bitstamp operate under regulatory oversight and are more likely to have robust security measures and insurance coverage than unregulated offshore platforms.
Withdraw regularly. Make it a habit to move funds off exchanges after completing trades. The longer your crypto sits on someone else’s platform, the longer it’s exposed to risks you can’t control.
This week’s Coinbase outage is a perfect example. Users couldn’t access their funds for over six hours because of a hardware failure at an Amazon data centre. If your crypto had been in a personal wallet, the outage wouldn’t have affected you at all.
Step 6: Watch Out for DeFi Risks
DeFi offers incredible opportunities but it also introduces risks that don’t exist in traditional finance.
Check audit reports. Before depositing funds into any DeFi protocol, check whether it has been audited by a reputable security firm like CertiK, Trail of Bits, or OpenZeppelin. An audit doesn’t guarantee safety, but a protocol that hasn’t been audited at all is a much bigger gamble.
Be careful with bridges. Cross-chain bridges, which move assets between different blockchains, have been the source of some of the largest hacks in crypto history. The Drift and Kelp exploits both targeted bridge infrastructure. If you must use a bridge, choose one built on established infrastructure like Chainlink’s CCIP and keep the amount to what you can afford to lose.
Revoke unused approvals. When you interact with a DeFi protocol, you often give it permission to access tokens in your wallet. If that protocol is later compromised, the attacker can use those approvals to drain your funds even if you’ve already withdrawn your deposit. Tools like Revoke.cash let you review and remove old approvals.
Start small. When trying a new protocol for the first time, test it with a small amount before committing significant funds. This limits your downside if something goes wrong.
Step 7: Recognise and Avoid Scams
Crypto scams have evolved far beyond the obvious “send me 1 BTC and I’ll send you 2 back” tricks. Modern scams are sophisticated, well-designed, and often target experienced users.
Fake support messages. If you post about a problem on social media, scammers will immediately DM you pretending to be official support staff. No legitimate company provides customer support through unsolicited direct messages.
Fake airdrops and token approvals. Random tokens appearing in your wallet are often bait. Interacting with them can trigger malicious smart contracts that drain your real holdings. If you didn’t expect it, don’t touch it.
Impersonation websites. Scammers create pixel-perfect copies of popular exchanges and wallet sites with slightly different URLs. Always bookmark the real URLs of the sites you use and navigate to them directly rather than clicking links from emails, social media, or search ads.
Romance and investment scams. Someone you met online convinces you to invest in a “guaranteed return” platform. You deposit funds, see fake profits on a dashboard, and then discover you can’t withdraw. These scams have stolen billions and are growing rapidly in 2026.
The golden rule: if it sounds too good to be true, it is. No legitimate investment guarantees returns. No real exchange needs you to deposit crypto to “unlock” your account. And no one who genuinely cares about you will pressure you to invest quickly before you’ve had time to think.
Step 8: Build Good Habits
Security isn’t a one-time setup. It’s a set of habits you practice every time you interact with crypto.
Verify before you sign. Before approving any transaction in your wallet, read what you’re signing. Check the contract address. Check the amount. If anything looks unfamiliar, reject it and investigate.
Keep software updated. Wallet apps, browser extensions, and operating systems should always be running the latest version. Updates often include security patches for newly discovered vulnerabilities.
Use a dedicated device. If you hold significant amounts of crypto, consider using a dedicated computer or phone exclusively for crypto transactions. This reduces the risk of malware from casual browsing, downloads, or gaming.
Stay informed. Follow trusted security researchers on X, subscribe to security alert services, and pay attention to reports about new scams and exploits. The crypto security landscape changes constantly, and staying informed is one of the best defences available.
The Bottom Line
Crypto gives you something that traditional finance doesn’t: complete control over your own money. But with that control comes complete responsibility for keeping it safe.
The steps in this guide aren’t complicated. Use a hardware wallet for long-term storage. Protect your seed phrase. Enable 2FA everywhere. Don’t leave funds on exchanges longer than necessary. Be sceptical of everything that asks for your money or your credentials.
FAQ
What is the safest way to store cryptocurrency?
A hardware wallet like Ledger or Trezor is the safest option for long-term storage. It keeps your private keys on a physical device that never connects to the internet, making remote theft virtually impossible. For everyday transactions, a reputable software wallet like Phantom or MetaMask paired with strong 2FA is sufficient for smaller amounts.
What should I do if I think my wallet has been compromised?
Immediately transfer any remaining funds to a new wallet with a completely new seed phrase. Do not reuse any credentials from the compromised wallet. Revoke all token approvals from the affected address using a tool like Revoke.cash. Report the incident to any exchanges where you have accounts, and consider filing a report with local authorities.
How can I tell if a crypto website or message is a scam?
Legitimate companies will never ask for your seed phrase, private keys, or passwords through email, DMs, or pop-ups. Always verify website URLs by checking them against bookmarked addresses rather than clicking links. Be suspicious of unsolicited messages offering help, guaranteed returns, or urgent requests for action. When in doubt, go directly to the official website and contact support through verified channels.
Disclaimer: This article is for informational purposes only and does not constitute financial advice. Cryptocurrency investments carry significant risk. Always conduct your own research before making any investment decisions.