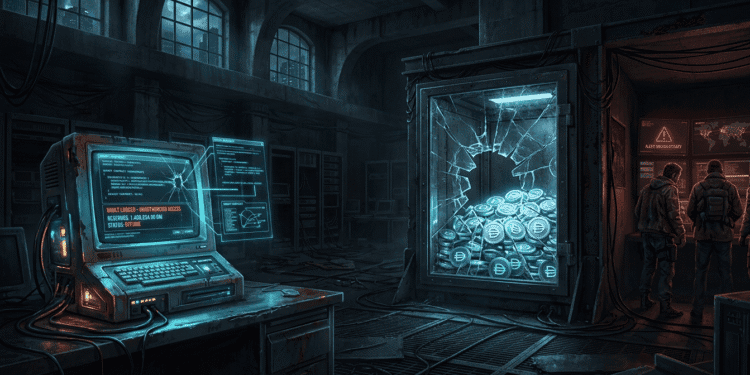
Transit Finance lost about $1.8 million in DAI after attackers exploited a legacy smart contract that had been deployed on TRON and deprecated after 2022, creating another warning sign for DeFi teams that old code can remain dangerous long after it has been replaced.
The team said the incident affected a small number of users who had interacted with the outdated contract, while the current version of Transit’s smart contract remains unaffected. Transit also said it completed investigation, isolation, and remediation work by May 12, and affected users will receive full compensation through a plan to be announced on official channels.
Security trackers placed the loss near $1.88 million in DAI. The stolen funds were later identified in a single Ethereum wallet, showing how the attack moved from an old TRON-side contract issue into Ethereum-based stablecoin holdings.
Why the Transit Finance Exploit Matters
Transit Finance is known for Transit Swap, a decentralized exchange aggregator that helps users find routes for token swaps across different networks. Aggregators are useful because they can compare liquidity and pricing across multiple sources, but that same cross-chain design can create more places where something can go wrong.
The latest exploit matters because it did not hit Transit’s current main contract version. Instead, the problem came from a legacy TRON contract that had already been deprecated. That makes the case more worrying for the wider DeFi market because it shows that old infrastructure can still create losses if users, permissions, or funds remain exposed.
DeFi teams often move fast. They upgrade contracts, add chains, retire old code, and launch new versions. But smart contracts do not disappear just because a newer version exists. If an old contract is still reachable, still approved by users, or still connected to some part of the system, attackers may continue looking for a way in.
What Happened in the TRON Contract Exploit?
Transit Finance said the issue came from an early-version smart contract that was originally deployed on TRON and deprecated in 2022. After discovering the problem, the team said it isolated the affected components and carried out additional review and remediation work.
That timeline is important because the project is trying to separate the legacy issue from its current operating system. Transit said its current contract version has remained secure and has operated for more than four years with regular audits and monitoring. The team also told users that no action is required from them at this stage.
The exploit still created a real loss. The amount was not small, and the use of DAI makes the stolen value easier to track than a volatile token that changes sharply in price. Reports tied the stolen funds to a wallet beginning with 0x8a6, where about 1.875 million DAI was identified after the attack.
The cleaner way to understand the incident is this: Transit’s newer system was not the reported weak point, but an older contract connected to past usage still became an attack path. That is exactly the kind of hidden risk that many DeFi users do not see when they interact with protocols over several years.
TRANSIT FINANCE LOSES 1.88M USD IN HACK TIED TO 2022 LEGACY TRON CONTRACT
Cross-chain DeFi protocol Transit Finance (@TransitFinance) was exploited on Tuesday for roughly $1.88 million, with stolen funds now sitting in DAI on Ethereum after originating on TRON, according to… pic.twitter.com/XhUrMXDA0h
— BSCN (@BSCNews) May 13, 2026
Why Legacy Contracts Are Still a DeFi Problem
Old smart contracts can be hard to manage because blockchain systems are usually designed to be permanent. Once a contract is deployed, it may keep existing on-chain even if the project stops using it publicly.
That creates a long-tail security problem. A team can launch a better version, update its website, and tell users to move to newer contracts, but attackers can still inspect old code. If users have left token approvals in place, or if old functions remain callable, a deprecated contract can become a quiet target.
This is one reason wallet approval hygiene matters. Users often approve contracts to spend tokens during swaps, bridges, or DeFi interactions. Those approvals may remain active unless the user revokes them. If an old contract later becomes vulnerable, a forgotten approval can turn into a real loss.
For projects, the lesson is broader. Deprecating a contract is not the same as safely retiring it. Teams need clear shutdown processes, user warnings, monitoring, approval cleanup guidance, and on-chain controls where possible. DeFi security is not only about protecting the newest product version. It is also about closing the doors left open by older versions.
Transit Promises Full Compensation
Transit Finance has promised to fully compensate affected users, which is an important step for restoring trust after the exploit. The team has not yet shared the full reimbursement schedule, but it said details will come through official channels.
That matters because compensation can be the difference between a contained incident and a reputational crisis. Users may accept that smart contract risk exists, but they expect teams to communicate clearly when funds are lost. In this case, Transit moved quickly to say the current contract was not affected and that users would not need to take action themselves.
The team also warned users to watch out for impersonators. That warning is important after any exploit because scammers often use the confusion to target victims a second time. Fake support accounts, fake refund links, and malicious “claim” pages can appear quickly after a public security incident.
Users should only follow updates from official Transit Finance channels and should never share private keys, seed phrases, or wallet recovery words. A real refund process should not require handing over secret wallet information.
How This Fits Into Transit’s Security History
Transit Finance has dealt with major security problems before, which makes this latest incident more sensitive.
In October 2022, Transit Swap suffered a much larger exploit involving roughly $28.9 million after an issue in its swap mechanism allowed unauthorized transfers from users who had granted approvals. A large portion of those funds was later recovered, but the case became one of the better-known DEX aggregator incidents from that period.
The new exploit is smaller, but it still raises fair questions about long-term contract management. Users will want to know how the old TRON contract remained exploitable, which wallets were affected, how compensation will be calculated, and what steps will prevent similar legacy risks from appearing again.
To Transit’s credit, the team has said the current contract version remains secure and that the issue was isolated. Still, the market is likely to judge the response by how quickly users are reimbursed and how clearly the project explains the root cause.
Security teams can fix code, but trust is rebuilt through transparency.
What Users Should Do Now
Transit has said no action is required from affected users, but that does not mean users should ignore their own wallet safety.
Anyone who has used Transit Swap, especially older versions or TRON-side contracts, should watch official project updates and consider reviewing old token approvals. Revoking unused approvals is a good habit across DeFi, not just for Transit users.
Users should also avoid rushing into links shared by strangers on X, Telegram, Discord, or email. After a hack, attackers often pretend to be support staff and offer fake reimbursement forms. Those scams can be more damaging than the original exploit if users sign malicious transactions or reveal recovery phrases.
For DeFi users in general, this incident is a reminder that security does not end when a protocol upgrades. If you interacted with older contracts, those old permissions may still matter.
Key Takeaway
Transit Finance’s $1.8 million DAI exploit shows that deprecated smart contracts can remain dangerous if they are still reachable or connected to old user permissions.
The team says its current contract version was not affected and has promised full compensation, which should help limit user damage. The larger lesson for DeFi is that retiring old code needs to be treated as a serious security process, not just a product update.
Disclaimer: This article is for informational purposes only and does not constitute financial, investment, or legal advice. Always conduct your own research before making any investment decisions.